Create bucket for storing MLflow artifacts and provide InfinStor service permission to access it¶
MLflow uses an s3 bucket to store artifacts. This bucket must be accessible to the InfinStor MLflow service so that the REST API and the UI can list artifacts, preview artifacts, etc. In order to make this possible there are a few steps that you must perform:
- Create a bucket for MLflow artifacts in your AWS account
- Create an IAM Policy with permission for exactly one task: read, write and list access to this bucket
- Create an IAM Role with the above policy for the InfinStor service to assume
Step 1: Create a bucket¶
Use a instructive name such as for-mlflow-artifacts or some such. In the example below, we are using the bucket name for-testing-freeservice
Please enable CORS access for the bucket as shown below, otherwise artifact listing and previewing in the MLflow UI will not work. To enable CORS support for the bucket, go to the AWS Console's S3 page, click on the bucket and choose the Permissions tab. Use the following policy to enable CORS support.
[
{
"AllowedHeaders": [
"*"
],
"AllowedMethods": [
"GET"
],
"AllowedOrigins": [
"*"
],
"ExposeHeaders": [],
"MaxAgeSeconds": 3600
}
]
Step 2: Create an IAM Policy that provides read, write and list access to the above bucket¶
Go to the IAM page of the AWS Console, and click on create policy. Use the json interface for entering the policy as show below.
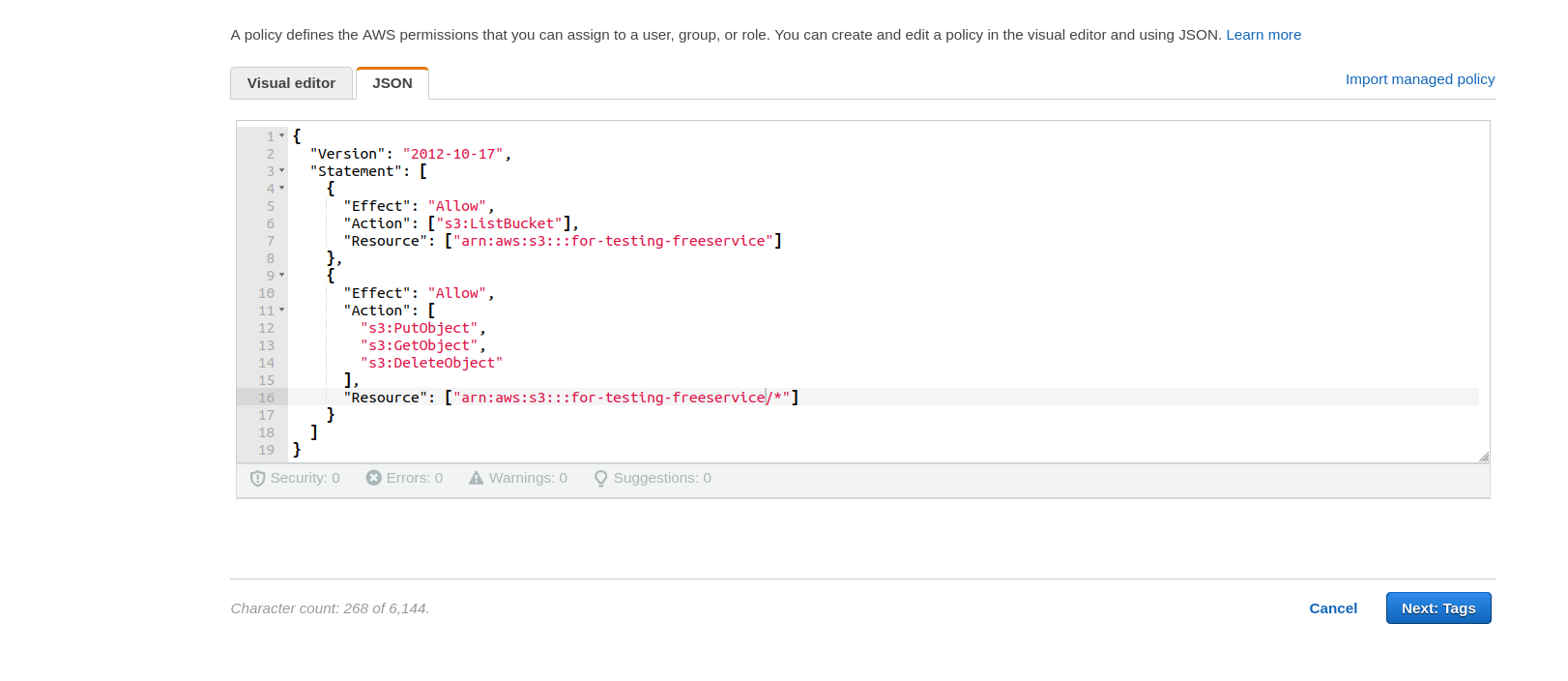
The policy that is suitable for this purpose is listed below. Replace for-testing-freeservice with your own bucketname in two places in the json.
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": ["s3:ListBucket"],
"Resource": ["arn:aws:s3:::for-testing-freeservice"]
},
{
"Effect": "Allow",
"Action": [
"s3:PutObject",
"s3:GetObject",
"s3:DeleteObject",
"s3:AbortMultipartUpload"
],
"Resource": ["arn:aws:s3:::for-testing-freeservice/*"]
}
]
}
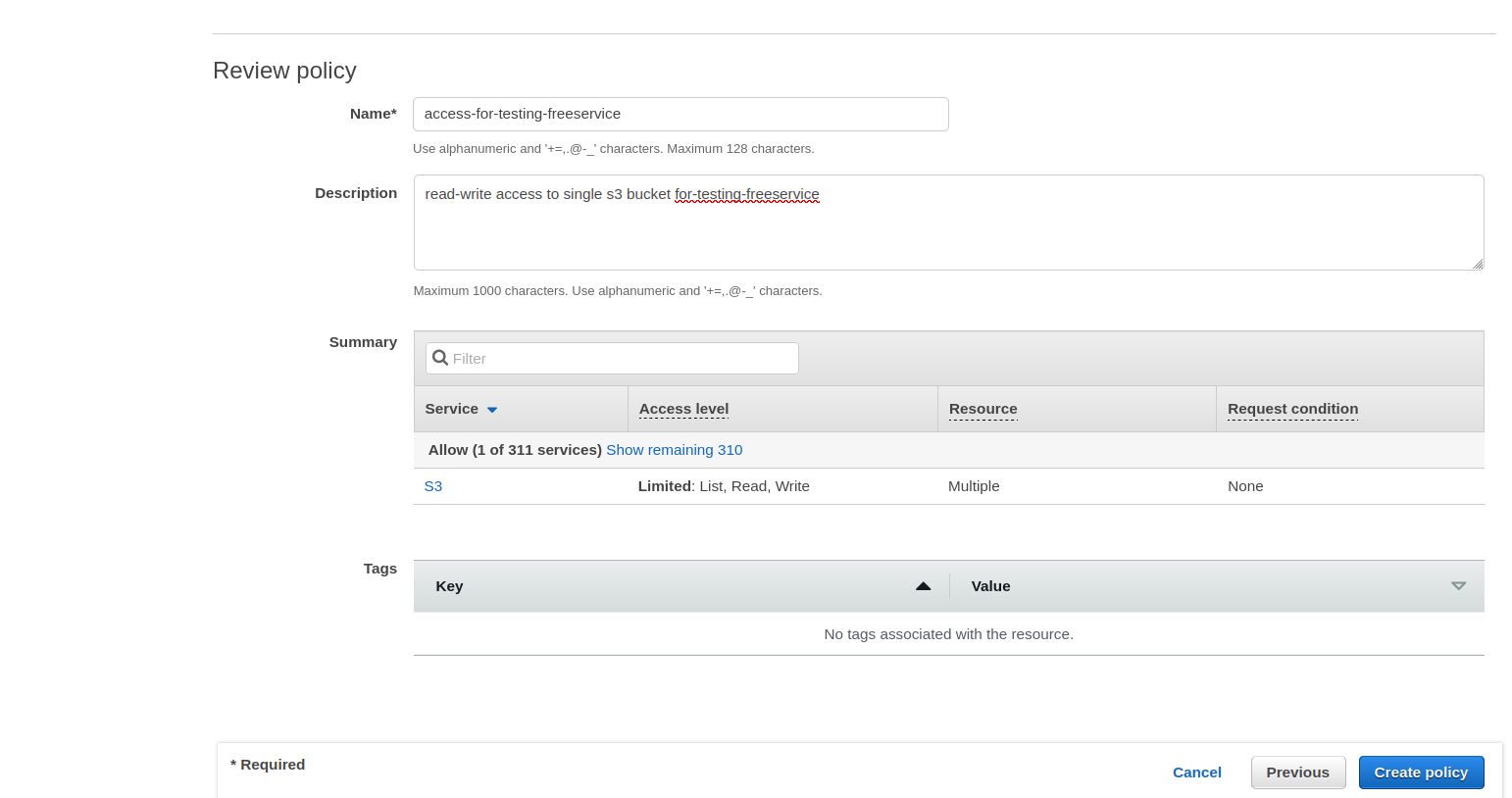
Next, in the review page, provide an instructive name for the policy and create it. In this example, we have used the name access-for-testing-freeservice
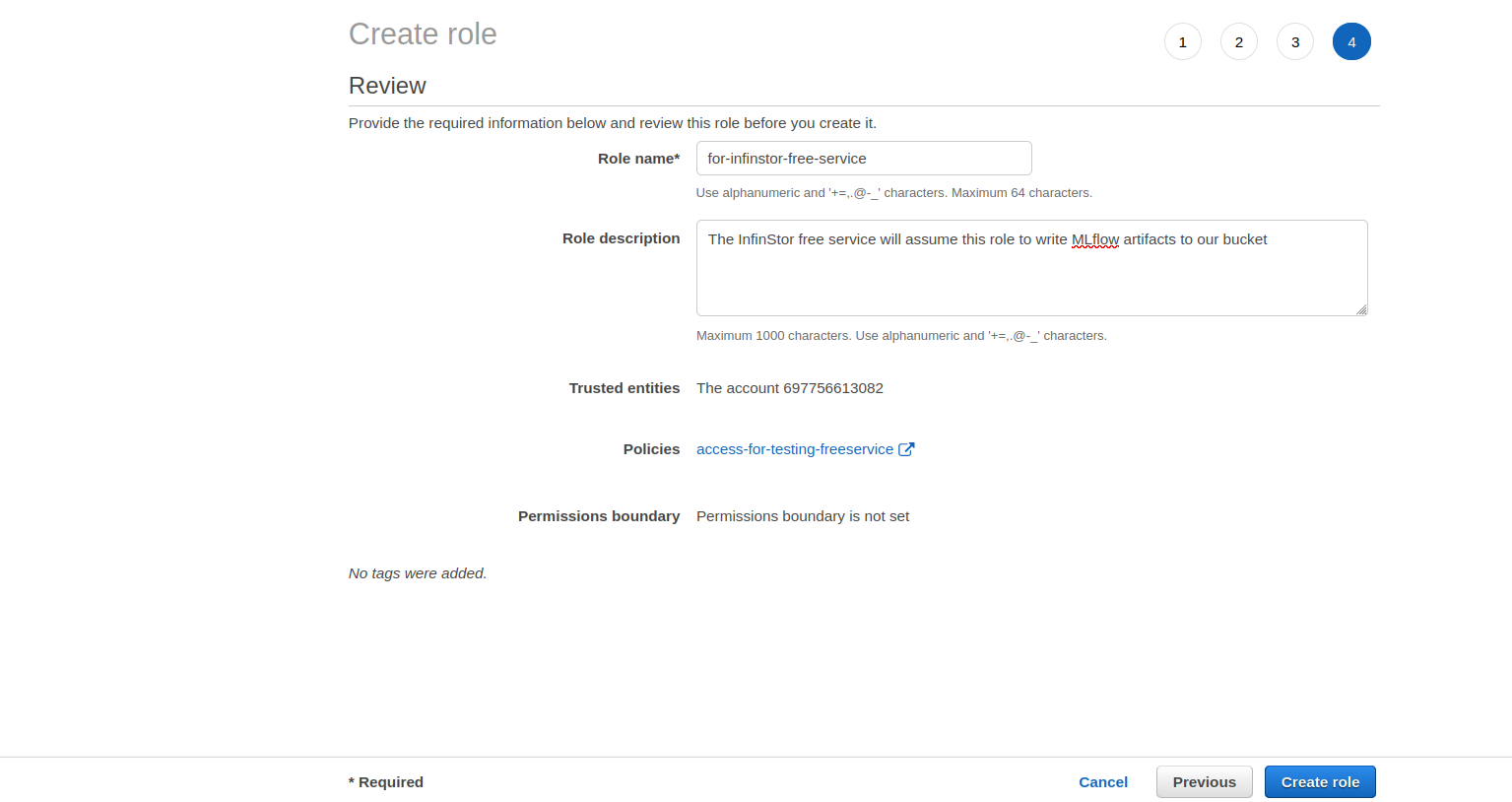
Step 3: Create an IAM Role with the above policy for the InfinStor service to assume¶
In the IAM page, choose create role and click on Another AWS Account as shown below. Please use the AWS account ID 697756613082 and choose your own External ID (this is similar to a password).
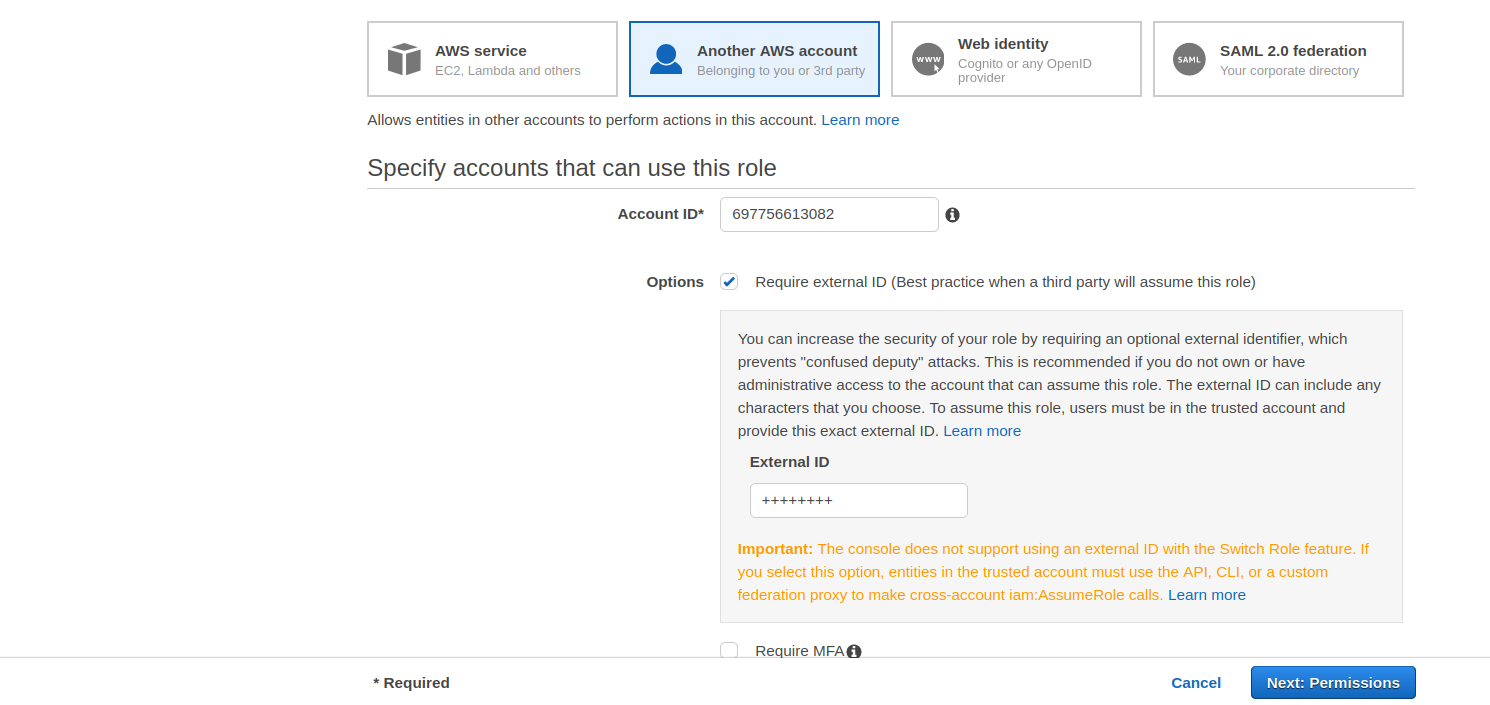
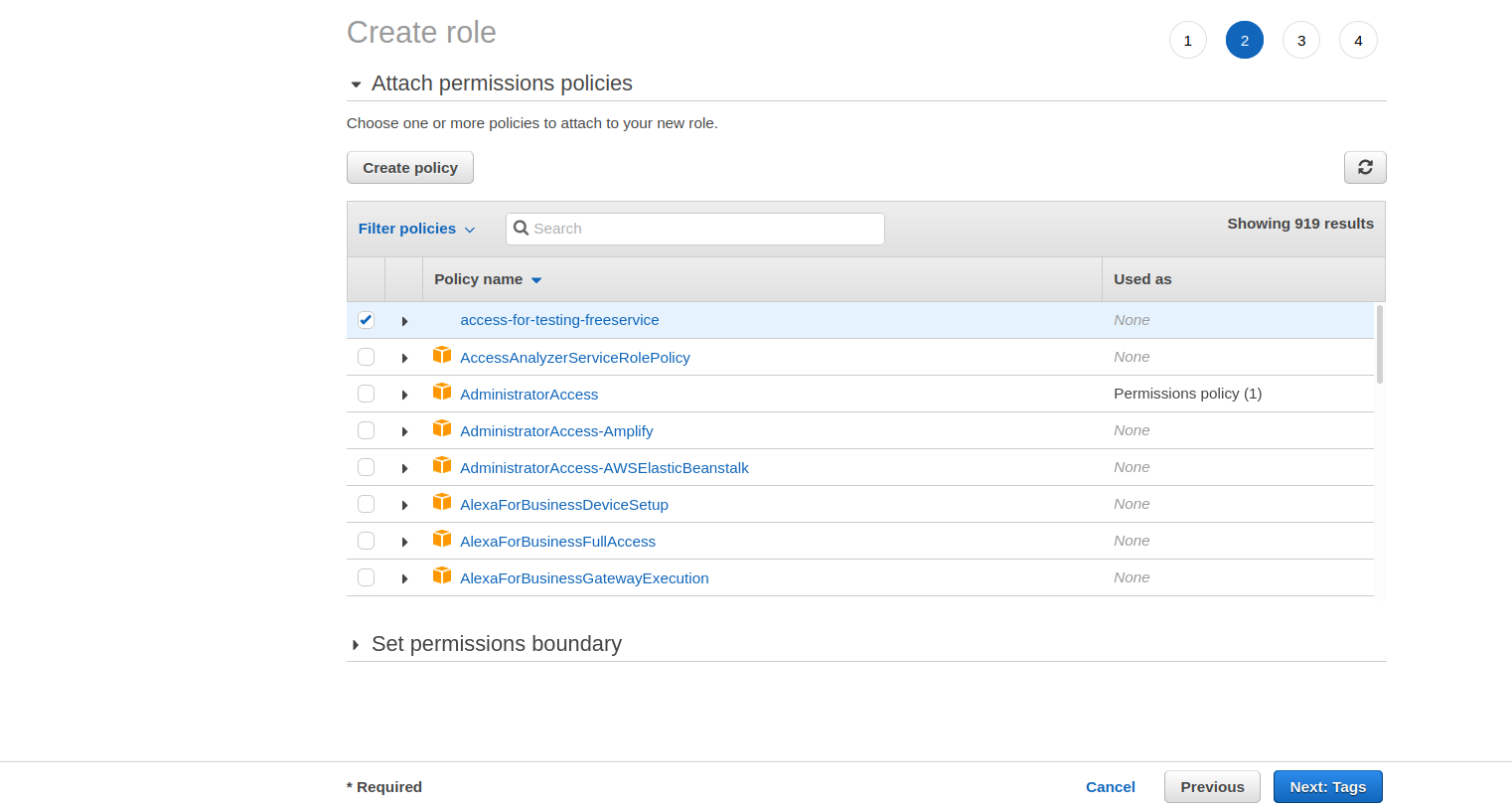
In the next page, you will need to select the policy created in step 2, e.g. access-for-testing-freeservice
Finally, provide a name for the role and create it.